[Security] Analysis of a Blackhole Exploit page
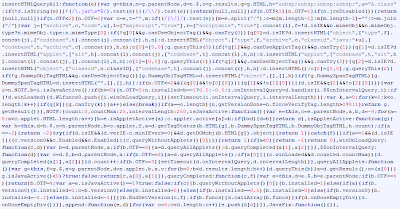
In this example, the exploit is heavily obfuscated. The exploit has been encoded and stored as HTML and JavaScript is used to decode the payload and run it.
Blackhole Exploit encoded ans stored in HTML
JavaScript decoding loop
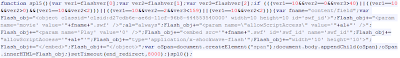
To decode the exploit, I used Malzilla, a popular JavaScript deobfuscation tool. Malzilla cannot manipulate the DOM like a real web browser, so I needed to copy and past the HTML-encoded data into a JavaScript variable. I then changed the JavaScript loop slightly, to extract the data from the variable instead of the HTML. Instead of doing an eval() of the code, I replaced the last line with document.write(c) to output the result.
The code below was delivered by Malzilla following the aforementioned adjustments (I've cut out the encoding data):
Modified code to run in Malzilla
I can now execute the script. The obfuscation requires many passes to fully decode the data andit takes quite a while to complete.
Script executed by Malzilla
Now, let's examine the output from Malzilla. The first part addresses a "Please wait page is loading..." message, very typical of the Blackhole Exploit kit so that the victim remains patient while the exploit code executes.
Then, the JavaScript figures out which browser is visiting the page, what plugins are installed and with which version. This is subsequently to decide which exploit payloads to deliver.
Browser fingerprinting
Depending on what browser information was obtained, different exploits can be delivered. It could for example be a malicious Java applet:
Launch a malicious Java applet
... or a remote code execution targeting a known Internet Explorer vulnerability:
MDAC exploit for Internet Explorer
.. or a malicious PDF file:
Malicious external PDF file
... or a malicious Flash file:
Malicious Flash file
Separating the exploit into an encoded payload and a decoding loop made it easier for the exploit kit creators to create an infinite array of different pages in order to evade detection. The Exploit kit is also more sophisticated than many other exploits as it is able to use the right exploit for each visitor.
[via]












Comments
Post a Comment
Để lại góp ý của bạn để blog của mình hoàn thiện hơn :))